7 Ways to Hack Instagram Account in 2020
Hello and Welcome back to my new Blog post, How to Hack Insragram Account in 2020. If You Like this Blog Share with your Friends for support us.
Instagram is one of the most popular social media apps today. But is it possible to hack Instagram username and password? Well, we live in a world of endless possibilities and hacking an Instagram profile is no exception. In this article, we look at several ways through which you can successfully break into any Instagram account.
However, keep in mind that hacking into another person’s Instagram account is illegal. This article is intended for entertainment purposes only and the tutorials contained here should only be used to get back your own IG account in case it is stolen or when you forget your password.
So without much further ado, let’s dive into the seven ways to hack an Instagram account successfully.
Table of Methods for Quick Navigating:
– Method 1: Using Keyloggers
– Method 2: Brute Force
– Method 3: Phishing
– Method 4: Password Reset
– Method 5: Creating a Fake Instagram App
– Method 6: Hacking a Facebook Account to Gain Access to Instagram
– Method 7: Hacking Instagram Account using Social Engineering Skills
Method 1: Using Keyloggers

You can use keyloggers to hack an Instagram account fast and easy. A keylogger is basically a special software program that can record your victim’s keyboard activity to the alphabet level and save the information in a file. This means that when your victim logs into Instagram with their username and password, the keylogger will save the details just for you. If you want to hack an account from a computer you can use Keylogger but since 95% of users access Instagram via mobile devices, we recommend using mobile keylogger apps such as mSpy, iKeyMonitor etc.
mSpy has been around for quite some time and keeps on adding new features every so often. The spy app gives you access to everything happening on Instagram including photos, messages, contact lists, videos and much more. The app has a keylogger feature that will allow you to easily hack your targeted victim’s Instagram password.
mSpy basically sends you all the media stored on the victim’s mobile phone. The application can even monitor and hack other platforms such as Snapchat, WhatsApp, Viber, and many more. Hacking Instagram via mSpy is currently available for both Android and iPhone devices. We’ve personally tested this app and can verify that it does work perfectly.
Download the mSpy app from internet
FlexiSpy is another high-quality spy program that can spy on Instagram and show you most of the activities taking place on the social media platform. It has the latest spying features for other popular social media platforms including Skype, Facebook, and Instagram. Another great thing about FlexiSpy is its call recording feature. It works in the same way as mSpy in hacking Instagram passwords.
Other popular spying apps include XNSPY and Mobistealth. Both cover Instagram in their spying capabilities and can be used on iPhones and Android devices. Hacking Instagram using any of the abovementioned apps is quite easy. All you need to do is buy the software license online, download the app and install it on the phone or device that you plan to hack, and then watch all the reports including logging details being relayed on your online dashboard. You don’t have to be near the hacked person. You can access the data from anywhere in the world as long as you have an Internet connection.
These spy programs allow you to hack into any Instagram account without the account owner’s knowledge. All you need to do is find a way to install the program on the target phone and you’ll start getting all the reports remotely.
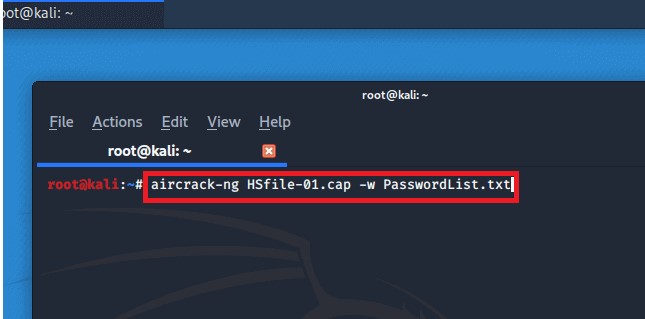
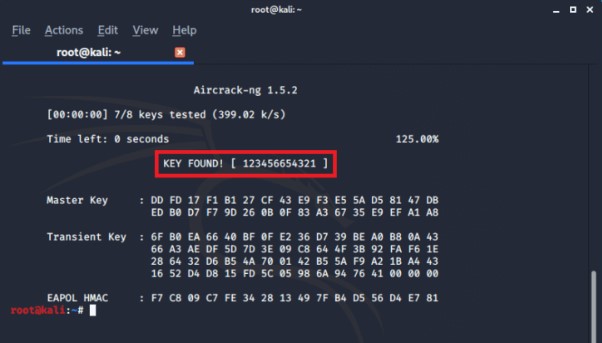
Method 2: Brute Force
Brute force basically refers to a hacking technique that tries to crack a password using every possible combination of phrases or words. The method usually uses a list based on a given input to crack the password. The brute-force method requires special cracking software made specifically for password cracking purposes. One of the most popular password cracking software is InstaRipper.
InstaRipper, available at InstaRipper.com, is an app that every Instagram user deserves to have, or at least know about. It has a powerful password cracking feature that can allow you to recover your lost password within a few minutes. However, the authors of the program clearly state that they will not be held responsible for any illegal activity that users may perform using the tool, such as hacking other people’s accounts without the account owners’ consent.
InstaRipper uses a modified version of brute force to crack passwords. The secret to its success lies inside the tool’s complex code. InstaRipper comes with a customized add-on in its code. This is because Instagram blocks your IP address after you try to log in several times without success, which is basically how brute-force works.
To avoid Instagram from blocking your IP, the tool comes with a mask feature that allows it to change to new fresh IPs after a few failed login attempts. It does this automatically without arousing Instagram’s attention. InstaRipper has its own VPN server that provides it with virtual IP addresses to allow you unlimited cracking attempts. Want to learn more about InstaRipper? It’s a user-friendly and easy-to-use software program that works on all modern devices including mobile and desktop devices. It supports Windows, Mac, Android, and iOS platforms.
Method 3: Phishing

Phishing is an old hacking method but still works like a charm today. It’s still a popular hacking trick that helps you figure out someone’s Instagram login details. So what is phishing all about?
Phishing involves creating a fake website that looks exactly as the real login page of a popular website such as Instagram. You can gain access to someone’s Instagram account when they enter their passwords and usernames on this fake page. This is possible because you created this fake page to capture all the data that the tricked user enters into the page. You have full control over the page and the data entered by the users.
To hack an Instagram account using phishing methods, you have to start by creating a fake Instagram login page and send it to the user you intend to hack. When the target logs in via this fake page, their private login details are saved on a file and the victim is redirected to a real Instagram login page. They’ll never know that they have just revealed their login details to you.
There are many ways of creating a fake Instagram login page but the easiest one we know so far is via Z-Shadow. Simply go to Z-Shadow, open a new account and then log in to your account. Scroll down and click to get to page three which shows a wide range of pages you can clone. Instagram is number 35 on the list. Simply copy the link and paste it on a new tab then press enter to see the Instagram clone page you’ve created. If anyone logs in via this page, you’ll capture their login details including passwords. You’ll find the passwords in your Z-Shadow account when you click on My Victim. It’s an easy and effective way of hacking Instagram passwords. All you need to do is to send the unsuspecting victim to your fake login page.
Method 4: Password Reset
In this method, you only need to have physical access to the targeted person’s phone to access his or her account. You simply get the person’s phone, open the Instagram app, and request for a password reset. An SMS will immediately be sent to the phone allowing you to set a new password. This method is also used to steal someone else’s Instagram account forever but can still be used to hack into the account temporarily. If you can access your victim’s phone, email account, or Facebook account, you can easily request a password reset from Instagram and hack the account instantly.
Method 5: Creating a Fake Instagram App
If you can already create a fake Instagram login page in Method 3 above, then why not create a fake Instagram app that looks exactly like the original and collect users’ data from the app? It is easy to create an Instagram clone app if you have the necessary skills or the patience and time to learn Android Application development. Once you have built your app, the remaining job is to make sure your victim downloads the fake app on their phone and uses it to log in to Instagram. Make sure the app redirects the targeted person to the real Instagram login page after you’ve collected their data in order to avoid raising any suspicion.
Method 6: Hacking a Facebook Account to Gain Access to Instagram

A majority of Instagram users have linked their Accounts with Facebook. If you can hack someone’s FB account, then you can easily gain access into their Instagram account. There are several ways of hacking into a Facebook account.
One of the most popular methods of hacking a FB profile is through Spyzie, a powerful mobile spy application. Spyzie is an extremely useful tool that helps you hack any Facebook password easily. You can even use the tool to hack any Gmail account besides FB and gain access to the victim’s Instagram account.
Another popular Facebook cracking program is Face Geek. You can easily hack anyone’s FB account using Face Geek as long as you have the person’s Facebook username. Face Geek is also available free of charge. Once you have hacked the victim’s Facebook account, you’ll then gain access to their Instagram account.
Method 7: Hacking Instagram Account using Social Engineering Skills

The basic concept in social engineering is to trick your victims to tell you their username and password indirectly. Social engineering has been around for years. It is an art of making people to actually give you specific information that you are looking for rather than use brute force or spy apps to get the information.
Most social engineering tricks are used to get the victim’s username and password combination for a specific website. You can apply the same social engineering skills to acquire the Instagram username and password from your targeted victim and use the data to gain access into their Instagram account. Most social engineering skills typically imitate a representative from the platform, in this case Instagram, who contacts you about a breach in the company’s security which has made it necessary for all users to change their passwords. They’ll even ask you to provide a unique password for your account.
Most Instagram social engineering tactics work 50% of the time in the real world. All it takes to succeed in social engineering is to have a good understanding of your victim’s typical behavior and what kind of password they’d set for their account. You’d be surprised by the number of people who use their names, their pet’s name, or girlfriend’s phone number as their password. Most people are quite predictable once you get to know them well.
Social engineering is not only restricted to guessing passwords. You can use the tactic to drive your potential victim to a fake phishing page that you have specifically created to collect passwords. You have to convince the person to log in their account via your page through social engineering. People love free things. You could entice them to your page with the promise of a freebie.
Another good example is the use of Spoof Calls. Spoof calls allow you to change a mobile number to anything. You can even prank a person by calling them using their own number. One of the best spoof calls website is SpoofCard. It is a paid service and illegal in some countries such as India. SpoofCard gives you a platform to put your social engineering skills to practice through the phone.
Finalizing
So we hope you’ve learned something new today. Keep in mind to never hack Instagram account which doesn’t belong to you, as this is not ethical and may bring you into trouble. So stay on safe side and use this information just for personal needs.
If you want daily hacking tutorial and want to learn ethical hacking then Join our telegram channel and also we are sharing free udemy courses, so don’t forget to join.




















.png)
%20(1).png)


.png)

.png)